A cyber-attack is any malicious attempt by an individual or a group to gain unauthorized access to a computer system or network. Usually, cyber-attacks aim to disrupt, destroy or alter the victims’ system or network. Cybercriminals also steal, expose or destroy private data from organizations which can be fatal for any business.
Today, regardless of size, cybersecurity is a key area of focus for all businesses. This can be attributed to the increase in the number and frequency of cyber-attacks being reported by companies worldwide. Since the pandemic struck in 2020, cyber-attacks have increased due to remote work. Statistics show that cyber crimes increased by 125% in 2021 and continued to rise from 2022 to today.
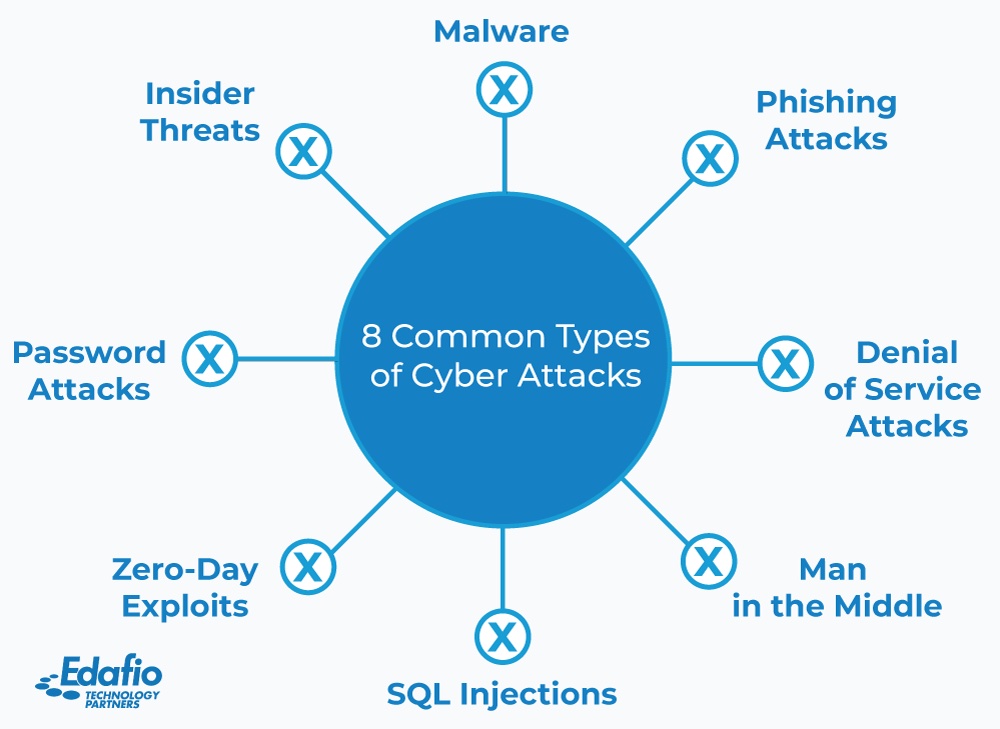
There are different types of cyber-attacks. Below we look at the most common cybersecurity attacks facing businesses today.
Malware
Malware is the generic term for malicious software. Malicious software is created to identify vulnerabilities in the system or network and target them to breach the system or network. Malware disrupts, destroys, and alters the network of the victim.
Here are some of the common malicious software:
Viruses – Viruses are self-replicating software that attaches to programs and files and are triggered when opened. They spread through your system without your knowledge slowing it down and destroying your data.
Ransomware – Ransomware is software that blocks access to some important components of your system until you pay the attackers a ransom. This software encrypts files on your system, locking you out until the attacker’s demands are met.
Spyware – This software spies on your system and network and sends this data to the attacker.
Adware – Adware software monitors users’ online activities, determining what ads to display on their screens.
Trojan – A Trojan is malicious software that seems to be legitimate.
Others include; worms, rootkits, and keyloggers.
Phishing Attacks
Phishing attacks are the most common type of cyber-attacks. The cybercriminal initiates communication with the victim while impersonating a trusted contact. Phishing attacks mostly involve fraudulent emails but can also be phone calls and texts that seem to come from credible sources such as an employer or a service provider.
The attackers aim to access sensitive information such as credit card details and passwords by tricking the victims into disclosing them. Phishing schemes also involve sending the victims malicious links. Clicking the link installs malware in the system.
Denial of Service Attacks (DoS)
A Denial of Service Attack occurs when the hacker or cybercriminals direct overwhelming traffic to a server or a system exhausting all the resources. As a result, the system shuts down, and legitimate users cannot access the system or network. Hackers can also use multiple devices/ botnets to direct traffic to a system shutting it down. This attack is known as a Distributed Denial of Service Attack(DDoS).
DoS attackers seek to slow down and eventually shut down your system, denying customers access and service. Most Social Media platforms have been victims of DoS and DDoS attacks leaving users out of the system.
Man in the Middle (MITM) Attacks
In a Man-in-the-Middle attack, the cybercriminal intercepts communication between two parties. This attack is also known as the eavesdropping attack, as the attacker joins the two-party conversation without their notice to steal information from your conversation.
The MitM attacks mostly occur when using insecure public WiFis or a compromised router. Hackers can insert themselves into the conversation between the visitor and the network. MitM can also happen in the case of malware, which will allow the hacker to install spying software that allows them to monitor the victim’s information.
Attackers can intercept communication between two parties to filter and steal private information such as usernames and passwords. Hackers also use MitM attacks to redirect conversations toward what they want by pretending to be the party you were talking to.
SQL Injection
SQL injection is the most common type of code injection attack. An attacker injects a malicious SQL code into an SQL-driven system. This gives the hacker access to sensitive information that the system would not disclose otherwise. The attacker can steal, modify or delete the information once they gain access.
Most data-driven websites use SQL to store sensitive data such as login details and account information. Hence, an SQL attack on these websites can lead to theft and breach of critical data. In 2021, over 70GB of data was stolen from the Gab website via SQL injection, revealing clients’ passwords and information.
Zero-Day Exploit
A Zero-Day Exploit is a type of attack that occurs on a system or network after a vulnerability in the system is announced. Attackers target and exploit the vulnerability disclosed before a patch is designed. They can breach into the system to steal data or make changes.
Password Attacks
A password attack is when the attacker tries to access an account by guessing or stealing the user’s password. In password-spraying attacks, the attacker tries the same password for many accounts. In brute force attacks, criminals use software that tries a combination of different usernames and passwords until they get the correct details.
Hackers can also try to get your password and login information through social engineering schemes such as email phishing, chats, and calls. To avoid falling victim to password attacks, it is important to use different usernames and passwords on different sites. Also, be aware of being tricked into disclosing your details.
Insider Threats
Employees and other parties in organizations have access to the system and important information. Different levels in the company have different access privileges and access to the company information and data. Some of these parties might decide to use their information and privileges for malicious reasons. Therefore, an organization needs to be aware of internal threats and not just focus on outside attacks.
Edafio – Your Cybersecurity Partners
Edafio has a team of cybersecurity experts who will offer you quality services regarding the security of your business. Our experts are always available and hold your information at utmost confidentiality.
Reach out to Edafio for an assessment of your business security or a cybersecurity plan for your business.
READY TO GET STARTED?
Make an Informed, Scalable Decision with Edafio