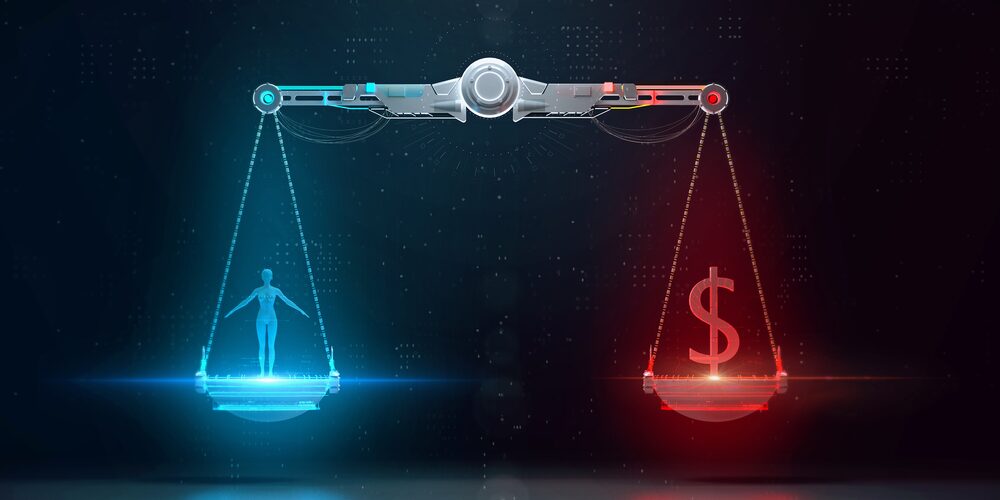
In 2022, the average cost of a data breach reached $4.4 million: a 13% increase since 2020. Based on the end of 2022, the average cost is expected to reach $5 million per incident in 2023. It is the role of IT consulting professionals to help businesses evaluate their own set of risk factors. Cybersecurity services are responding with awareness training, customized risk assessments, and protocols for a post-breach response.
Costs Associated With Data Breaches
Businesses can suffer the impact of a data breach for years. Some of the costs include network downtime, lost productivity, legal liability, business disruption, lost data, and lost intellectual property. There are also costs associated with a damaged reputation for the business. In 2020, IBM reported that personal customer data accounted for 80% of data breaches, costing $180 per record.
These costs are often difficult to plan for. One study found that 60% of small businesses fail in the six months following a cyberattack. While many small and medium-sized businesses have taken a “wait and see” approach to cybersecurity, the risks have increased. Of course, the risks are unique to your own business, and many factors impact your risk level.
Factors Impacting Your Risk Level
Types of Data
Many businesses are charged with the responsibility of protecting business data, employee data, and consumer data. Some of this data includes credit card information, phone numbers, email addresses, social media accounts, and anonymous customer data. While some information may seem more sensitive, all of it is meant to be confidential.
In the previously mentioned report from IBM, it was found that the type of data breach impacted the associated costs. If a data breach happened unintentionally, the costs to the business were lower. An intentional cyberattack led to a 16.6% higher cost per record.
Industry
Some industries have higher cybersecurity risks. The healthcare and financial industries are responsible for a lot of sensitive data, and the costs of a cyberattack are often higher. Energy companies and pharmaceutical companies are also at high risk. While lower, the impacts on retail businesses have also been on the rise.
Notification Laws
Your location matters. In the United States, every state sets its own laws for handling a data breach. The Arkansas Personal Information Protection Act requires businesses in the state to use security measures to protect the data they collect. The law also requires that, in the event of a data breach, affected individuals be informed within a reasonable timeline.
Notification laws are meant to give affected individuals an opportunity to take protective measures against threats like identity theft. These types of laws do make data breaches more public. They also mean businesses or other organizations may need to pay settlements to those affected. For example, the Little Rock school district agreed to a $250,000 settlement after suffering a very public data breach.
A Strong Cybersecurity Service Lowers Your Risk
The 2020 report from IBM emphasized the importance of two main factors that lead to data breaches. One is a total lack of cybersecurity automation or security measures that didn’t meet up with the business’s risk level. Too many small businesses believe that installing any firewall will be enough to protect them from a data breach. Companies today need services like awareness training, software management, and risk assessment.
The other major factor was a need for incident response protocols. Businesses have been failing to notice their data breaches, sometimes for months. When they do realize unauthorized access has occurred, they don’t have a response plan or team ready to handle it. This gives bad actors unlimited time to gain data access and take the next steps.
How IT Consulting Professionals Work to Lower Data Breach Costs
The main goal of any cybersecurity plan is to prevent a data breach from occurring. IT professionals need to take steps that can help lower the costs of a data breach.
Noticing the Data Breach
Too often, months go by before businesses notice a data breach. When a data breach goes unnoticed, the authorized access can continue. This can mean a greater loss of data and a more difficult time discovering the original cause of the breach. It can also mean a greater loss of trust with your clients when the breach is eventually reported.
A cybersecurity service will have measures in place to help notice a data breach. They will also have quicker response times. This is in large part because they will have a post-breach protocol in place. This helps companies minimize the damages from a data breach.
Regular Security Risk Assessments
One of the best ways to know where your business stands with cybersecurity is to consult with an IT professional. They can write up a full IT risk assessment. This includes finding vulnerabilities and measuring your business’s greatest exposure risks.
Hopefully, your business will only grow with time. A risk management plan should account for this and include plans for scaling. This should include a timing frequency plan that notes how often you’ll need a new risk assessment.
Security Awareness Training
Do your employees know the importance of difficult-to-decipher passwords? Do they know the latest tactics being used by threat actors in phishing schemes? Socially engineered cyberattacks are becoming more common and a lot more difficult to detect. With appropriate and regular training, you can be sure your employees know how to spot a possible attack.
The more employees you have, the higher your risk of phishing attacks. Appropriate training from IT consultants gives employees the information they need. It also provides a trusted expert when they have questions about malicious links, odd emails, or unfamiliar risks. There are alternatives to tradtional programs like a cyber escape room challenge for a more interative and entertaining approah to maintaining a healthy cybersecure company
Limiting Access
It’s an unfortunate truth that many data breaches are simply accidental. This can look like an employee accidentally emailing confidential data to a mistyped email address. It can also look like an employee simply opening information they weren’t meant to have access to.
By limiting data access to only those who need it, these kinds of accidents can be avoided. This lowers the risk of unauthorized access and better protects the business without impacting productivity.
Updates
Software companies regularly release patches to address newly discovered vulnerabilities in their software. As part of your cybersecurity service, regular software updates are addressed. Legacy software that may no longer be in use should be discontinued, lowering the risks posed by outdated software.
Business leaders need to have their minds focused on innovation and daily business management. The threat of data breaches shouldn’t be a constant worry. To gain peace of mind and safety for your business, ensure you have a strong cybersecurity plan.
Contact Edafio Technology Partners today to learn more about our cybersecurity protection services.
READY TO GET STARTED?
Make an Informed, Scalable Decision with Edafio